
The received information is valued for the photos made by the FSEP employee, which contain full EXIF-data, including the indication of a precise date when photos were taken, reads the report.
Besides that, InformNapalm got the videos taken by the operative of the 'Mangust' special tasks unit of the Russian Federation's FSEP department in Rostov region. This agent has repeatedly visited Donbas to take part in combat.
Read alsoRussia building military base near Ukraine's Kharkiv region – investigation (photos)The FF hackers said they had tracked down the subject's personal data, which was confirmed based on the captured information on a postal note.
During the analysis of the data and additional monitoring, it was found that the owner of the photo and video archive is Reichenau Nikolai Vladimirovich (born on May 17, 1985).
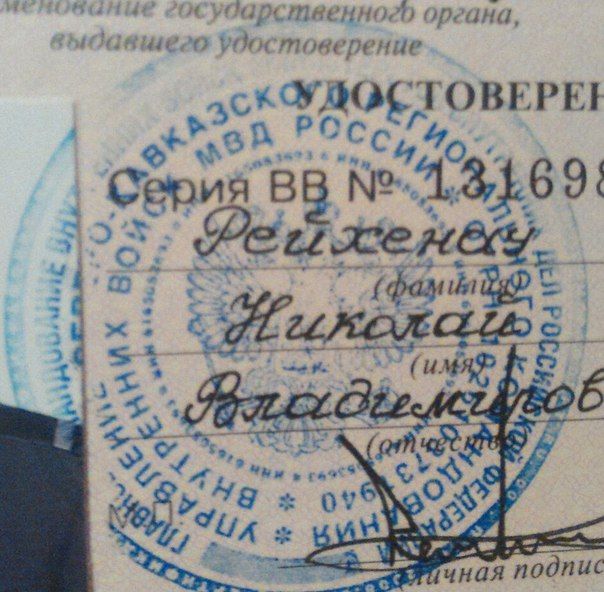
Hackers were also able to obtain copies of certain documents confirming his illegal presence in Donbas and analyze the geography of locations visited by the Russian operative. Based on the EXIF-data of the photos, InformNapalm restored the chronology of the man's visits to Donbas and the training base of the 'Mangust' special forces unit in Rostov region.
Read alsoOSINT proves Russia 200th motorized infantry brigade's participation in DonbasThe Russian operative's archives also contained photos and videos made in January of 2015 in the Donetsk airport – a series of so-called "materials for a report" about his "winter trip." One of the photos purports to show a killed Ukrainian soldier.
According to the report, all pictures and videos have been handed over to Ukraine's security forces.

